How do they use fake IDs for verification?
First of all, this is a very risky move as current banks and different foundations have cutting edge equipment to help with their confirmation cycles. You can also find it in their web-based help. In this way, it is very difficult to check your ledger with my god id.
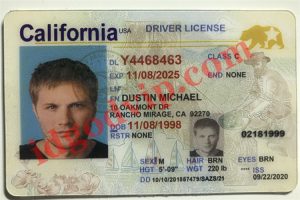
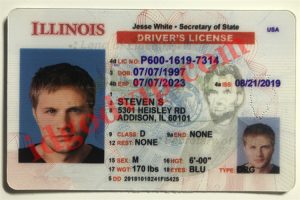
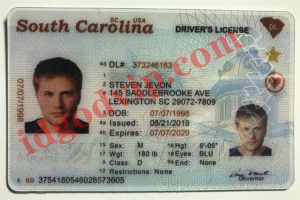
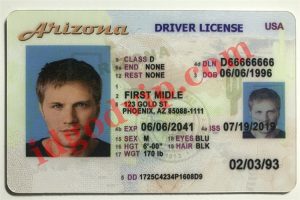
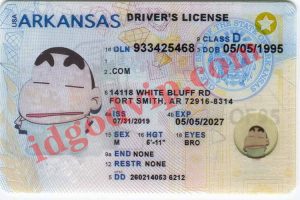
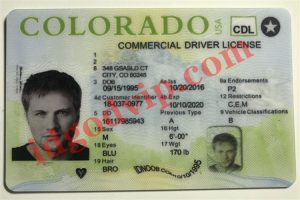
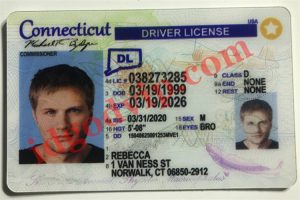
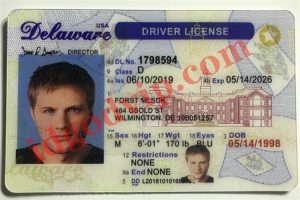
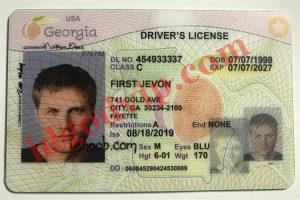
Yet many are still doing it. They buy the best fake ID cards from the famous idgod scannable fake ID producer (idgod.cz). The fake ID even appears to be a real ID with all the security components, including scanner tags, 3D images, and different components. Then, they also pre-arranged different profiles, which were additionally made; the fake IDs were guaranteed to be okay.
There is only one problem here. Where do they do dangerous fake ID verification? Those customers using the idgod fake id will find banks or financial institutions that have not yet used conventional techniques to confirm the identity of their customers. There is no innovative hardware at the monetary base level that can do this. Also, they are not using KYC interactions. The simple application and inspection process makes them powerless against fake IDs.
Shockingly, many banks still tolerate fake IDs without legitimate checks using KYC processes. Apart from the fact that they allow id god fake id clients to open records. The bank even issues visas, check cards and different authorities for this client.
Nonetheless, when they find out that you are using my god id, they will freeze your financial balance. They recommend that you send them your real ID to match the ID you used to open the record. In the most pessimistic case, an expert might examine your record. If they find serious infringement, you’ll have more problems.
all in all
The most common methods of using computer reasoning to perceive faces include artificial conscious computing and artificial intelligence. The calculations will investigate the eyes, eyebrows, nose, mouth, nostrils and iris. The framework uses this information to confirm that it is a human face. The AI computation then utilizes four different procedures to identify faces, including, appearance-based, information-based, and format coordination.
It reveals all the data about someone, so it provides the safest way to open records. This approach also limits the potential for monetary misconduct. However, it also has a negative side, which you should also take into account. For now, after you figure out the dangers and other data of the interaction, choose whether the idgod fake id is involved to confirm.